Modern applications are harder to observe than they used to be. A single request may traverse containers, cloud services, networks, and the Linux kernel before reaching the user. eBPF helps teams see what is happening across those layers with less manual instrumentation and lower operational friction.
What is eBPF?
eBPF is a Linux kernel technology that lets small, verified programs run within the kernel without modifying the kernel source code or loading custom kernel modules. It is widely used for networking, security, tracing, and observability.
For developers and platform teams, the main value is visibility. Instead of guessing what happens between an application, the network, and the operating system, eBPF can observe events close to where they happen.
That makes eBPF observability useful in modern systems where services are spread across containers, Kubernetes nodes, cloud instances, and different programming languages.
How eBPF Technology Works
eBPF programs attach to kernel events. These events can include network packets, system calls, file operations, or application-level activity exposed through probes.
Before an eBPF program runs, the Linux kernel verifier checks whether it is safe. The verifier analyzes the program to reduce risks such as unsafe memory access or uncontrolled loops.
A simple flow looks like this:
- A developer or tool loads an eBPF program.
- The kernel verifier checks it.
- The program attaches to a kernel event.
- When that event happens, the eBPF program collects or filters data.
- The result is sent to the user space for dashboards, alerts, or analysis.
Many eBPF systems also use just-in-time compilation, which helps programs run efficiently inside the kernel.
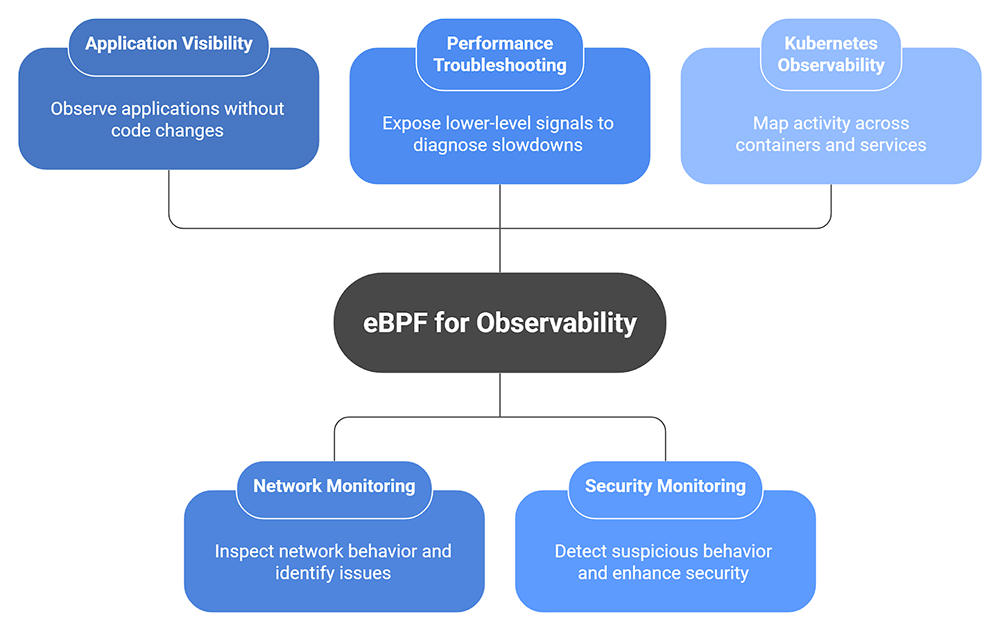
Top eBPF Use Cases for Observability and Performance Monitoring
eBPF is useful because it provides teams with deep visibility into applications, networks, and infrastructure without requiring significant code changes. This is especially helpful in Kubernetes and other distributed systems, where issues often occur across multiple layers simultaneously.
Application visibility without code changes
One of the strongest eBPF use cases is observing applications without deploying language-specific agents everywhere. eBPF can collect useful signals from the kernel, helping teams monitor services written in different languages. New Relic describes this as language-agnostic observability from the Linux kernel.
This is helpful when teams run legacy services, third-party software, or fast-moving microservices.
Network monitoring
eBPF can read much of the network data that other packet inspection tools capture. This visibility allows engineers to diagnose network latency, connection failures, packet drops, DNS resolution issues, and service-to-service communication issues. This is useful in Kubernetes, where network paths can change quickly as well.
Performance troubleshooting
When an application slows down, the problem isn’t always in the code. It may stem from disk I/O, CPU scheduling, memory pressure, network retries, or system calls.
eBPF does a great job of visualizing deep coordination primitives that many backend systems exhibit. This allows engineering teams to quickly correlate symptoms and diagnose the underlying system behavior.
Security monitoring
Security teams use eBPF to observe suspicious behavior such as unexpected process execution, file access, network connections, or privilege changes. Since eBPF works close to the kernel, it can provide strong runtime visibility.
Kubernetes and container observability
Containers add another layer between the application and the infrastructure. eBPF helps map what is happening across pods, nodes, and services without relying only on application logs.
This is why eBPF observability has become popular in cloud-native environments.
Final Thoughts
eBPF is improving modern observability by providing teams with more system-level insight without requiring more complex application code. It won’t replace logs, metrics, and traces, but it can help each become more valuable by communicating what is happening at the OS, network, and runtime layers.
FAQs
1. How does eBPF improve observability compared to traditional kernel instrumentation methods?
Usually, observability requires the application (and sometimes the system) to be significantly modified to add observability agents and kernel modules. eBPF can provide low-level observability without requiring a kernel module, adding observability agents, or significant changes to an application. When eBPF programs are loaded into the system, they are verified, which helps keep the system more secure.
2. What are the most common eBPF use cases in production environments today?
Current uses for eBPF include network observability, observability in Kubernetes, observability for application performance, real-time security, tracing system calls, and application (and/or system) network observability. It helps in understanding how distributed modern systems behave, flow, and consume resources.
3. Is eBPF safe to run in production, and what security controls should teams apply?
eBPF can be safe in production when managed properly. The kernel verifier checks programs before execution, but teams should still restrict who can load eBPF programs, use trusted tools, keep kernels up to date, review permissions, and monitor eBPF activity as part of their security process.
4. How does eBPF-based observability impact application performance and system overhead?
eBPF-based observability usually has low overhead because it collects data close to the source and can filter events before sending them to user space. Still, overhead depends on the tool, event volume, kernel version, and configuration. Teams should test it under a realistic, production-like load.